These docs are for Cribl Edge 4.0 and are no longer actively maintained.
See the latest version (4.17).
Roles
Define and manage access-control Roles and Policies
Cribl Edge offers role-based access control (RBAC) to serve these common enterprise goals:
Security: Limit the blast radius of inadvertent or intentional errors, by restricting each user’s actions to their needed scope within the application.
Accountability: Ensure compliance, by restricting read and write access to sensitive data.
Operational efficiency: Match enterprise workflows, by delegating access over subsets of objects/resources to appropriate users and teams.
Role-based access control is enabled only on distributed deployments (Edge, Stream) with an Enterprise license. With other license types and/or single-instance deployments (Edge, Stream), all users will have full administrative privileges.
RBAC Concepts
Cribl Edge’s RBAC mechanism is designed around the following concepts, which you manage in the UI:
Roles: Logical entities that are associated with one or multiple Policies (groups of permissions). You use each Role to consistently apply these permissions to multiple Cribl Edge users.
Policies: A set of permissions. A Role that is granted a given Policy can access, or perform an action on, a specified Cribl Edge object or objects.
Permissions: Access rights to navigate to, view, change, or delete specified objects in Cribl Edge.
Users: You map Roles to Cribl Edge users in the same way that you map user groups to users in LDAP and other common access-control frameworks.
Users are independent Cribl Edge objects that you can configure even without RBAC enabled. For details, see Local Users.
How Cribl Edge RBAC Works
Cribl Edge RBAC is designed to grant arbitrary permissions over objects, attributes, and actions at arbitrary levels.
As of v. 2.4.x, Roles are customizable only down to the Worker Group/Fleet level. E.g., you can grant Edit permission on Worker Group/Fleet
WG1to User A and User B, but cannot grant them finer-grained permissions on child objects such as Pipelines, Routes, etc.
Cribl Edge’s UI will be presented differently to users who are assigned Roles that impose access restrictions. Controls will be visible but disabled, and search and log results will be limited, depending on each user’s permissions.
Access to the same objects via Cribl Edge’s API and CLI will be similarly filtered, with appropriate error reporting. E.g., if a user tries to commit and deploy changes on a Worker Group/Fleet where they are not authorized, they might receive a CLI error message like this: git commit-deploy command failed with err: Forbidden
Cribl Edge Roles can be integrated with external authorization/IAM mechanisms, such as LDAP and OIDC and mapped to their respective groups, tags, etc.
Using Roles
Cribl Edge ships with a set of default Roles, which you can supplement.
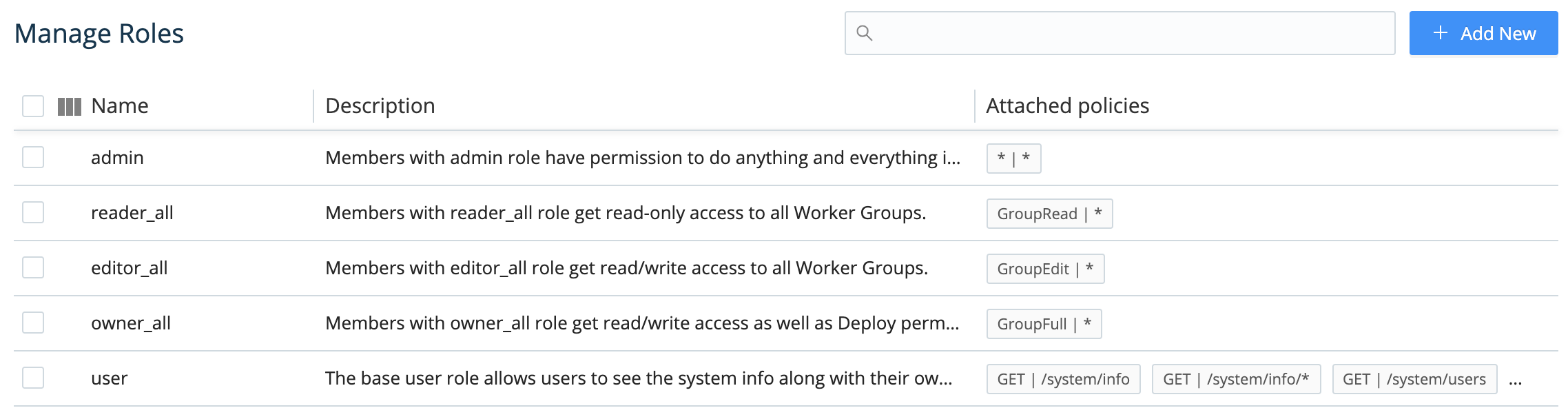
Default Roles
These Roles ship with Cribl Edge by default:
| Name | Description |
|---|---|
| admin | Superusers - authorized to do anything and everything in the system. |
| owner_all | Read/write access to (and Deploy permission on) all Worker Groups/Fleets. |
| editor_all | Read/write access to all Worker Groups/Fleets. |
| reader_all | Read-only access to all Worker Groups/Fleets. |
| collect_all | Ability to create, configure, and run Collection jobs on all Worker Groups/Fleets. |
| gitops | Ability to sync the Cribl Edge deployment to a remote Git repository. |
| notification_admin | Read/write access to all Notifications. |
| user | Default role that gets only a home/landing page to authenticate. This is a fallback for users who have not yet been assigned a higher role by an admin. |
Cribl strongly recommends that you do not edit or delete these default roles. However, you can readily clone them (see Clone Role below), and modify the duplicates to meet your needs.
Initial Installation or Upgrade
When you first install Cribl Edge with the prerequisites to enable RBAC (Enterprise license and distributed deployment), you will be granted the admin role. Using this role, you can then define and apply additional roles for other users.
You will similarly be granted the admin role upon upgrading an existing Cribl Edge installation from pre-2.4 versions to v. 2.4 or higher. This maintains backwards-compatible access to everything your organization has configured under the previous Cribl Edge version’s single role.
Adding and Modifying Roles
In a distributed environment, you manage Roles at the Leader level, for the entire deployment. On the Leader Node, select Settings > Global Settings > Access Management > Roles.
To add a new Role, click New Role at the upper right. To edit an existing Role, click anywhere on its row. Here again, either way, the resulting modal offers basically the same options.
The options at the modal’s top and bottom are nearly self-explanatory:
Role name: Unique name for this Role. Cannot contain spaces.
Description: Optional free-text description.
Delete Role: And…it’s gone. (But first, there’s a confirmation prompt. Also, you cannot delete a Role assigned to an active user.)
Clone Role: Opens a New role version of the modal, duplicating the Description and Policies of the Role you started with.
The modal’s central Policies section (described below) is its real working area.
Adding and Modifying Policies
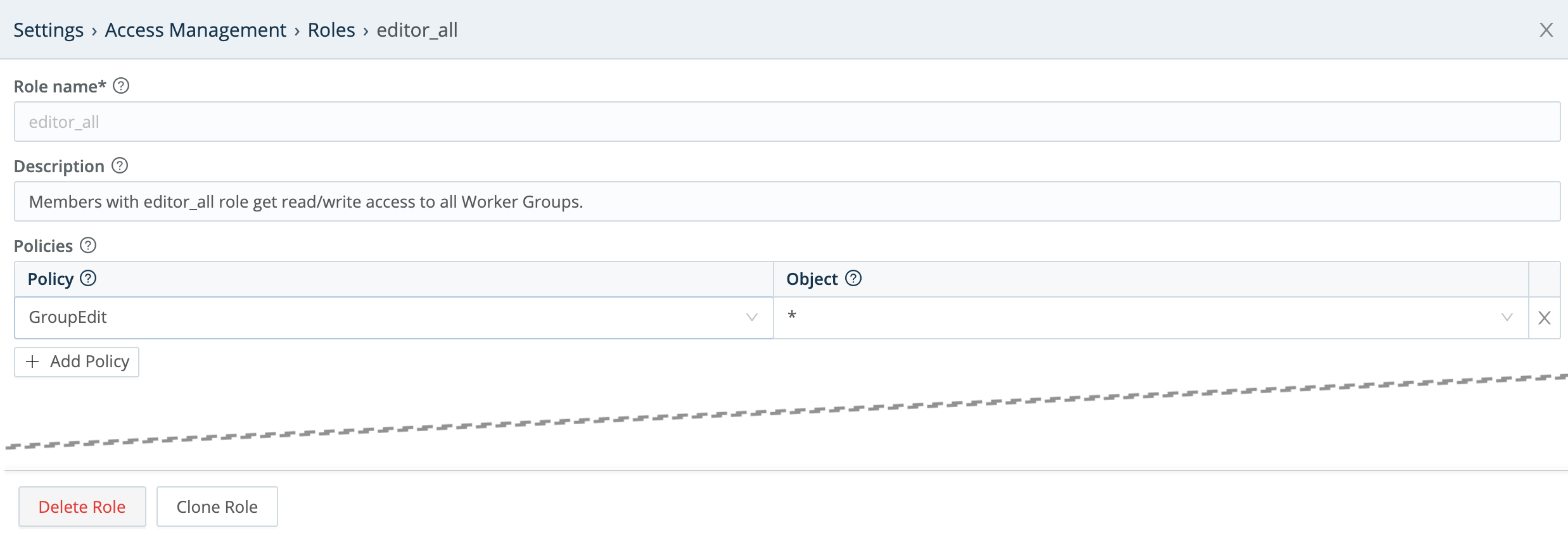
The Policies section is an expandable table. In each row, you select a Policy using the left drop-down, and apply that Policy to objects (i.e., assign permissions on those objects) using the right drop-down.
Let’s highlight an example from the above screen capture of Cribl Edges built-in Roles: The editor_all Role has the GroupEdit Policy, with permission to exercise it on any and all Worker Groups/Fleets (as indicated by the * wildcard).

To add a new Policy to a Role:
Click + Add Policy to add a new row to the Policies table.
Select a Policy from the left column drop-down.
Accept the default object on the right; or select one from the drop-down.
To modify an already-assigned Policy, just edit its row’s drop-downs in the Policies table.
To remove a Policy from the Role, click its close box at right.
In all cases, click Save to confirm your changes and close the modal.
Default Policies
In the Policies table’s left column, the drop-down offers the following default Policies:
| Name | Description |
|---|---|
GroupRead | The most basic Worker Group/Fleet-level permission. Enables users to view a Worker Group/Fleet and/or its configuration. |
GroupEdit | Building on GroupRead, grants the ability to also change and commit a Worker Group/Fleet’s configuration. |
GroupFull | Building on GroupEdit, grants the ability to also deploy a Worker Group/Fleet. |
GroupCollect | Grants the ability to create, configure, and run Collectors on a Worker Group/Fleet. |
* (wildcard) | Grants all permissions on associated objects. |
Objects and Permissions
In the Policies table’s right column, use the drop-down to select the Cribl Edge objects on which the left column’s Policy will apply. (Remember that in v. 2.4, the objects available for selection are specific Worker Groups/Fleets, or a wildcard representing all Worker Groups/Fleets.) For example:
Worker Group <id>NewGroup2default(Worker Group)*(all Worker Groups)
Extending Default Roles
Here’s a basic example that ties together the above concepts and facilities. It demonstrates how to add a Role whose permissions are restricted to a particular Worker Group/Fleet.
Here, we’ve cloned the editor_all Role that we unpacked above. We’ve named the clone editor_default.
We’ve kept the GroupEdit Policy from editor_all. But in the right column, we’re restricting its object permissions to the default Worker Group/Fleet that ships with Cribl Edge.
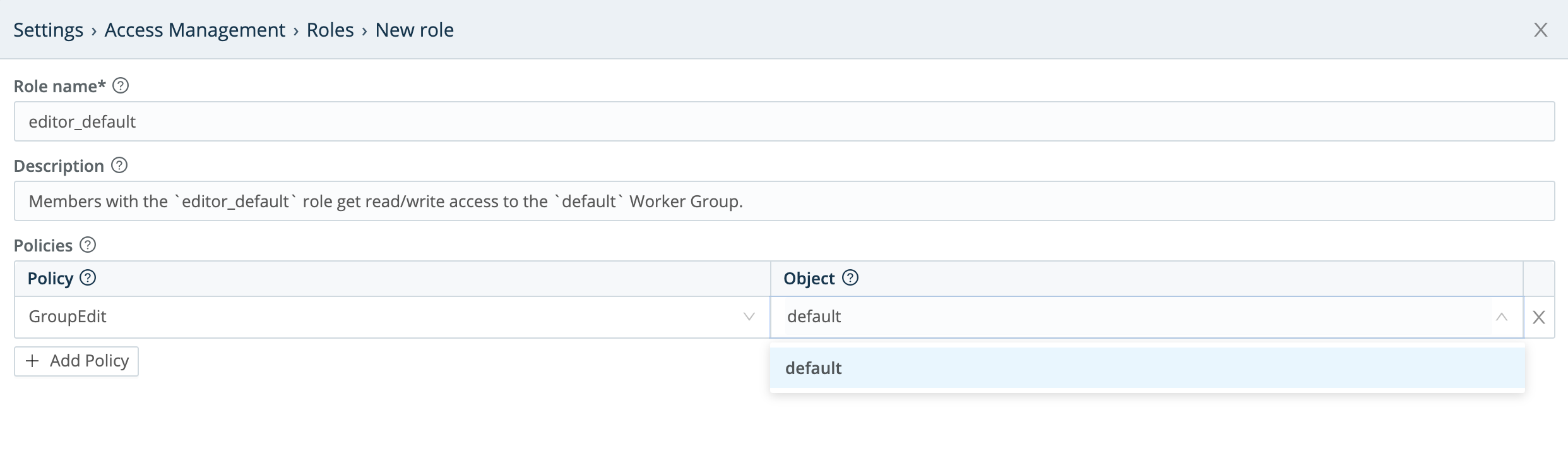
You can readily adapt this example to create a Role that has permissions on an arbitrarily named Worker Group/Fleet of your own.
Roles and Users
Once you’ve defined a Role, you can associate it with Cribl Edge users. On the Leader Node, select Settings > Global Settings > Access Management > Local Users. For details, see Local Users.
Note that when you assign multiple Roles to a given user, the Roles’ permissions are additive: This user is granted a superset of all the permissions contained in all the assigned Roles.
By default, Cribl Edge will log out a user upon a change in their assigned Roles. You can defeat this behavior at Settings > Global Settings > General Settings > API Server Settings > Advanced > Logout on roles change.
External Groups and Cribl Edge Roles
You can map user groups from external identity providers (LDAP, Splunk, or OIDC) to Cribl Edge Roles, as follows:
Select Settings > Global Settings > Access Management > Authentication.
From the Type drop-down, select LDAP, Splunk, or OpenID Connect, according to your needs.
On the resulting Authentication Settings page, configure your identity provider’s connection and other basics. (For configuration details, see the appropriate Authentication section.)
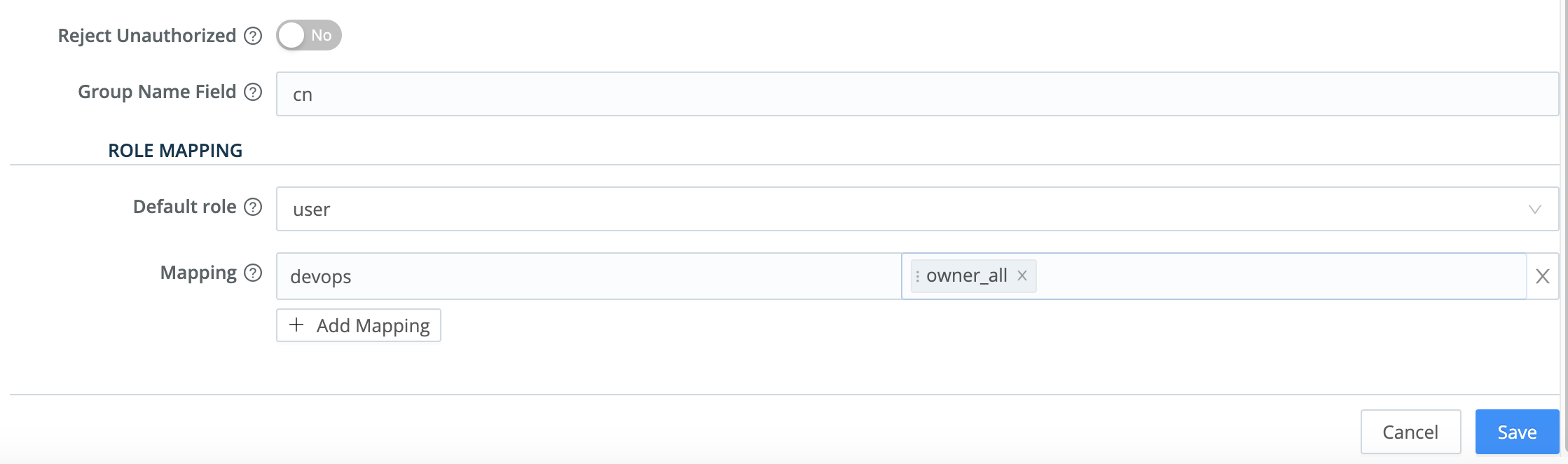
Under Role Mapping, first select a Cribl Edge Default role to apply to external user groups that have no explicit Cribl Edge mapping defined below.
Next, map external groups as you’ve configured them in your external identity provider (left field below) to Cribl Edge Roles (right drop-down list below).
To map more user groups, click + Add Mapping.
When your configuration is complete, click Save.
Here’s a composite showing the built-in Roles available on both the Default role and the Mapping drop-downs:
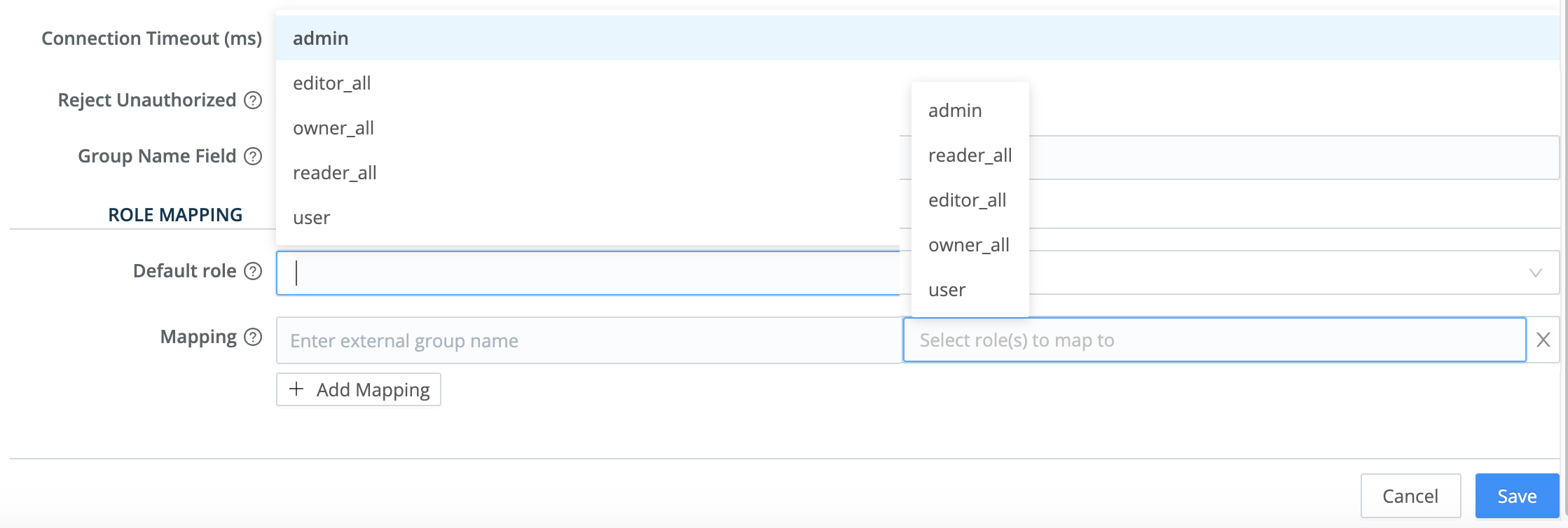
And here, we’ve set a conservative Default Role and one explicit Mapping: