These docs are for Cribl Stream 4.10 and are no longer actively maintained.
See the latest version (4.17).
Configuring SSO groups
In your IDP (identity provider), configure user groups that match Permissions for both Cribl.Cloud Organizations and individual products.
Linking IDP Groups with Teams
You can use Teams to automatically connect groups of Members with IDP users. This allows you to grant IDP users Workspace- or Product-level permissions.
For each Team, you can specify Mapping IDs to use as external IDs. In your IDP, create one or more groups with IDs listed in Mapping IDs to connect them to the Team and in this way automatically grant IDP users access with Workspace-level permissions.
To create a Team with an external ID, refer to Create a Team. To add an external ID to an existing Team:
- On the top bar, select Products, and then select Cribl.
- In the sidebar, select Organization, then Members & Teams, and then Teams.
- Select the Team you want to configure.
- In Mapping IDs, provide a list of external IDs for the Team.
- Confirm with Save.
Users added to a Team through Mapping IDs will not be listed in the Team Members table. Use your IDP to view the list of Users and manage them.
IDP Group Naming
If you are not using Teams, or want to grant Organization-level permissions to IDP users, you can define groups that will be mapped to Cribl Roles based on their names.
In such a case, the names you define for groups in your IDP must include Cribl and the Role name (Owner, Admin, or User).
They can include Organization or product name (Stream, Edge, or Search).
If they don’t contain a product name, the group is treated as an Organization name.
Even though IDP group names without Organization will be treated as Organization-level permissions, we recommend keeping Organization in the name for clarity.
You can use either the open or the closed format (with or without spaces) in group names. You can freely add prefixes or suffixes to Group Names that follow the formats in the examples above. Cribl will ignore these additions when mapping IDP groups to Cribl Roles. Examples:
SOME-LABEL-12345-CriblOrganizationOwnerCriblOrganizationEditor-420
| Cribl.Cloud Role/Permission | IDP Group Name |
|---|---|
| Owner | Cribl Organization Owner /or/ CriblOrganizationOwner /or/ Cribl Owner |
| Admin | Cribl Organization Admin /or/ CriblOrganizationAdmin /or/ Cribl Admin |
| User | Cribl Organization User /or/ CriblOrganizationUser /or/ Cribl User |
| Editor | (Deprecated, will be mapped to Admin) Cribl Organization Editor /or/ CriblOrganizationEditor |
| Read Only | (Deprecated, will be mapped to User) Cribl Organization Read Only /or/ CriblOrganizationReadOnly |
Default Product Permissions
When you map external users to your Cribl Organization, their initial product-level Permissions follow a different inheritance pattern than Members configured within Cribl. This is to avoid downgrading product-level Permissions that Organization-level Users might already have.
The defaults for mapped users are:
- Organization
OwnerorAdmininheritsAdminPermission on all products. - Organization
UserinheritsUserPermission on all products (except Cribl Lake, which inheritsNo Access). - Organization
Editor(deprecated) inheritededitorlegacy Roles on all products. - Organization
Read Only(deprecated) inheritedRead OnlyPermission on Stream and Edge, andUserPermission on Search.
Group Configuration Better Practices
- A Cribl.Cloud Organization’s Owner Role can be shared and transferred among multiple users. This facilitates gradual ownership transfers, corporate reorganizations, and other scenarios.
- Those users should be in both the Owner and Admin groups in your IDP. (This enables them to acquire all needed permissions across Cribl’s two corresponding Roles.)
- Aside from dual-assigning the Owners, you should assign every other user only one group in your IDP. (Cribl’s Admin and Editor Roles include all the permissions of the Roles below them.)
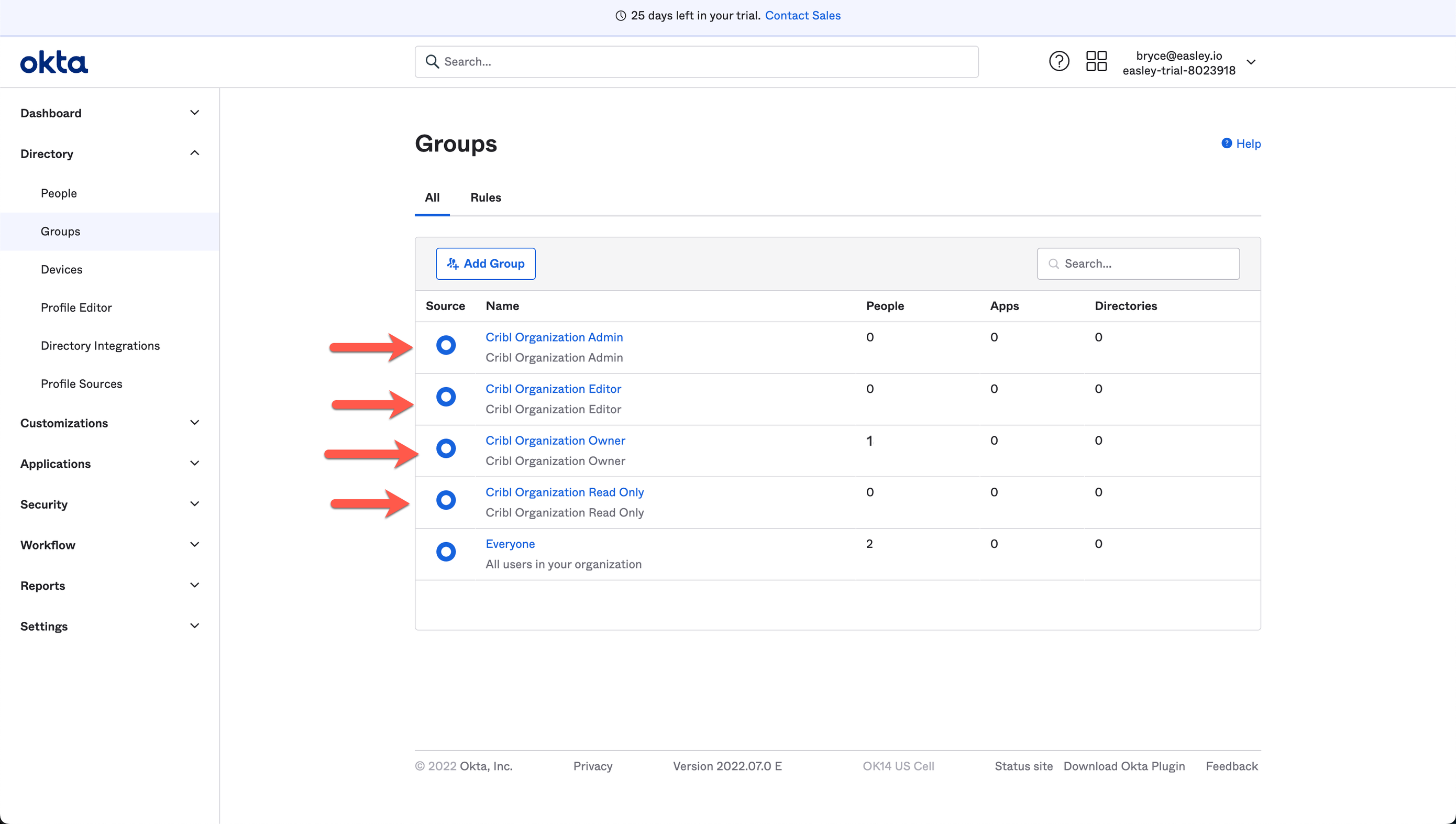
Here’s an example of how groups configuration (at an early stage) might look in Okta:
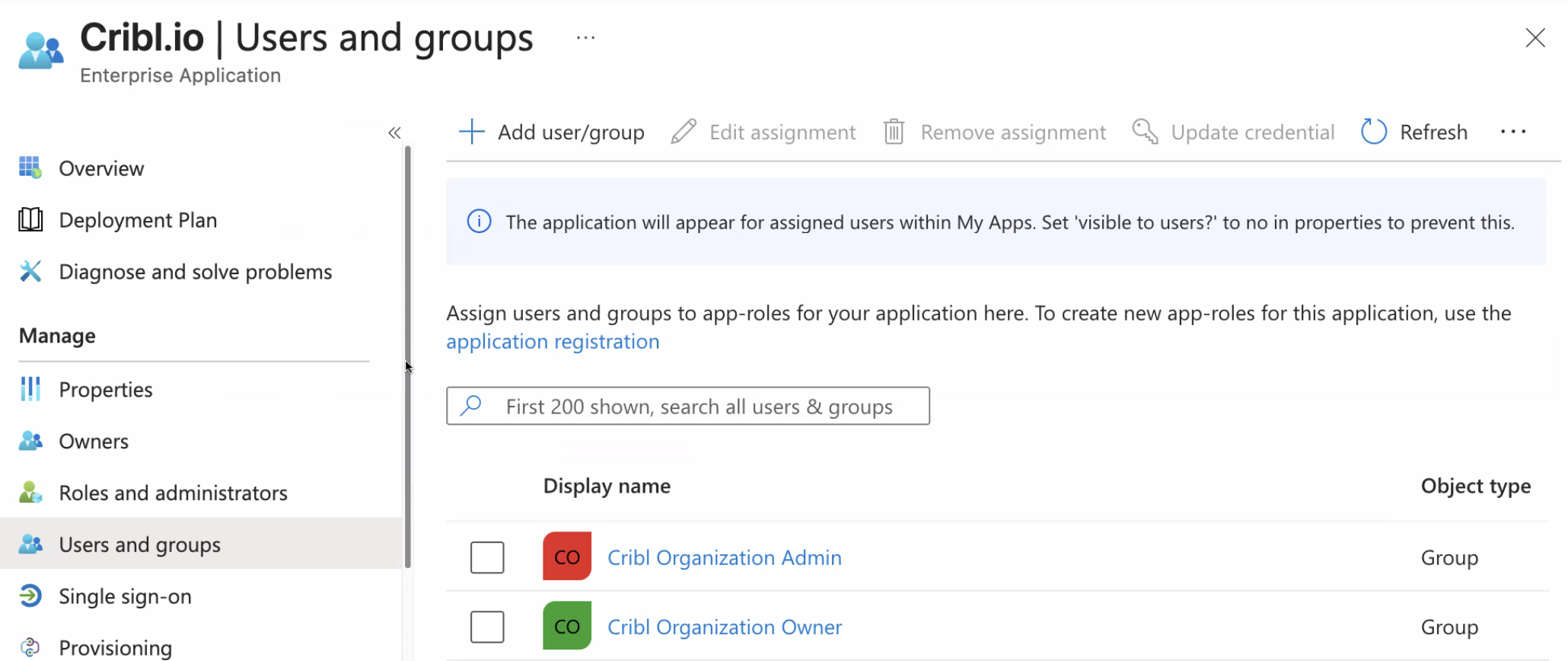
This example shows how groups configuration might look in Microsoft Entra ID: